The New Evolution of Security Operations
Securing your organization isn’t just an important initiative—it’s a race against time and sophistication. With thousands of cyber attacks occurring daily, security operations managers, engineers, analysts, and executives face a constant battle to keep their systems secure. Let’s delve into the key challenges these professionals encounter and explore how the Impelix IMPACT SecOps platform can transform their approach to cybersecurity.
The Relentless Volume of Cyber Attacks
The sheer volume of cyber attacks is staggering and relentless. According to a report by the University of Maryland, hackers attack every 39 seconds, on average 2,244 times a day. This overwhelming frequency demands that security teams spend a significant portion of their day dealing with alerts from multiple security products. Traditional methods of manual threat detection and response are simply not sustainable in this environment.
You need a security operations platform that integrates seamlessly with your existing security infrastructure, consolidates alerts, and provides a centralized view of your security landscape. This reduces the time spent on managing disparate systems, allowing your team to focus on the most critical threats.
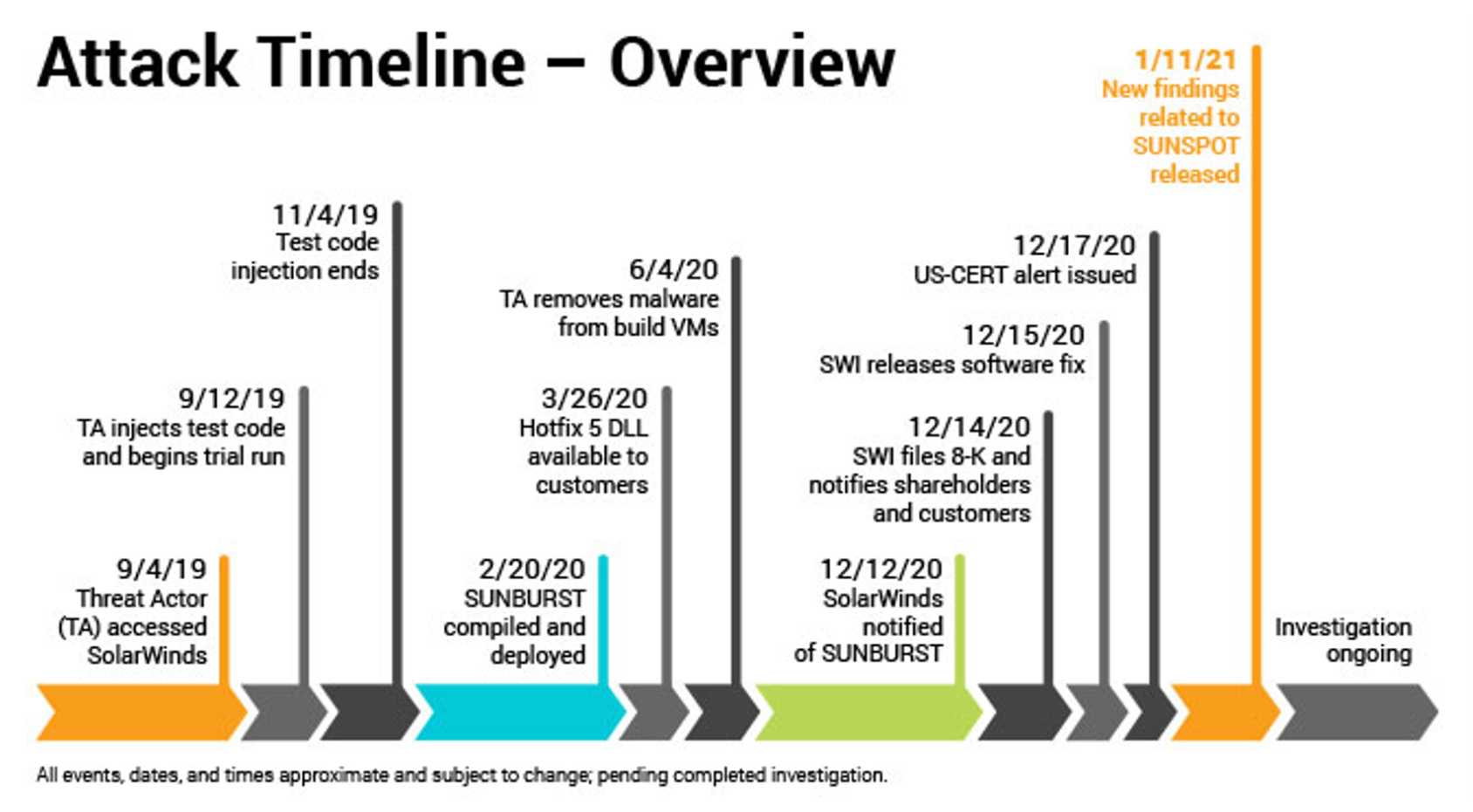
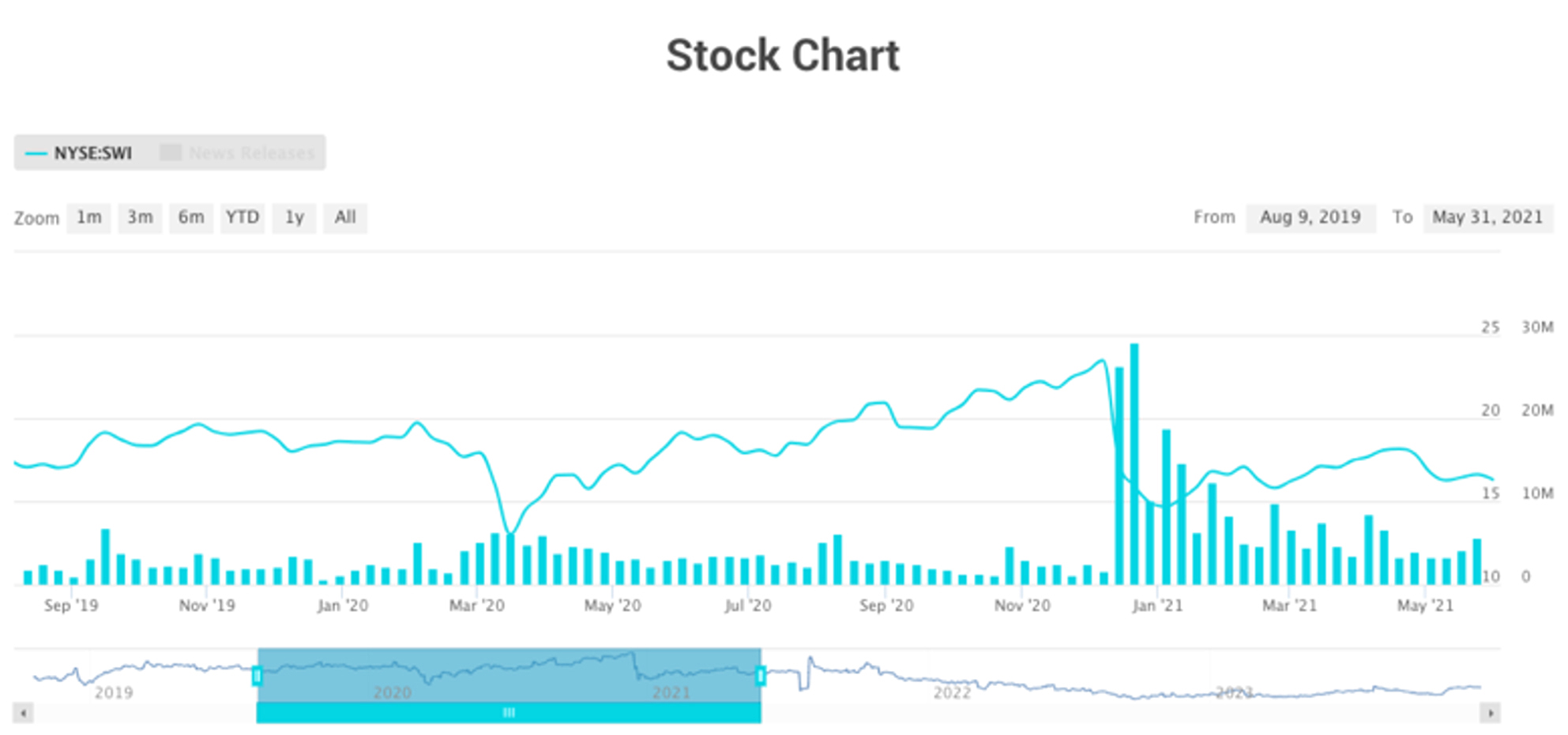
Time to Detect and Respond: Still Too High
In cybersecurity, every second counts. However, many organizations still struggle to detect and respond to threats swiftly. The 2023 Data Breach Investigations Report by Verizon highlights that the average time to identify a breach is 287 days. This delay can lead to significant financial and reputational damage.
Look for a security operations platform that leverages advanced machine learning algorithms with real-time analytics to dramatically reduce detection and response times. Automated incident response capabilities ensure that threats are neutralized before they can cause harm, transforming your security posture from reactive to proactive.
The Need for Automation and AI
Humans alone will never be able to keep up with the speed and volume of modern cyber threats. Automation and AI are no longer optional; they are essential components of a robust cybersecurity strategy. According to a report by IBM, organizations using AI and automation experienced a 27% faster response to cyber incidents.
Modern security operations software must be built with purpose-built AI-driven automation at its core. It will continuously learn from new threats and adapts to evolving attack patterns, ensuring your defenses are always a step ahead. This reduces the burden on your security team and allows them to focus on more strategic initiatives.
Lack of Visibility Across the Entire Attack Surface
One of the most significant challenges in cybersecurity is achieving comprehensive visibility across the entire attack surface. Without a holistic view, it’s nearly impossible to track threats in real time and understand the full scope of an incident.
More valuable than log aggregation, a holistic view should be achieved by integrating security and non-security data into incident story graphs to offer a detailed, real-time view of threat activity, enabling your team to quickly identify and mitigate risks across the entire attack surface.
Bridging the Cybersecurity Expertise Gap
The cybersecurity talent shortage is a well-documented issue. The (ISC)² Cybersecurity Workforce Study reports that the global shortage of cybersecurity professionals is nearly 3.5 million. Organizations are being asked to do more with less, and the expertise gap continues to widen.
The IMPACT platform is designed to amplify the capabilities of your existing team. With intuitive dashboards, advanced analytics, and automated workflows, even less experienced team members can effectively manage and respond to threats. This helps bridge the expertise gap and maximizes the efficiency of your security operations.
Empowering Your Team with Impelix IMPACT
At Impelix, we understand the challenges that security professionals face. That’s why we’ve developed the IMPACT platform—to tackle these issues head-on and empower your team with the tools and insights they need to stay ahead of threats and protect what matters most.
Key Features of IMPACT:
- Centralized Alert Management: Consolidates alerts from multiple sources, reducing noise and enabling quicker response.
- AI-Driven Automation: Automates threat detection and response, ensuring rapid mitigation.
- Real-Time Analytics: Provides actionable insights and comprehensive visibility across the entire attack surface.
- User-Friendly Interface: Intuitive design that enhances usability for all skill levels.
Ready to transform your security operations? Let’s connect and elevate your cybersecurity strategy together. With Impelix IMPACT, you can achieve a new level of security resilience and ensure that your organization is protected against the ever-evolving threat landscape.
Contact Us Today to learn more about how the IMPACT platform can revolutionize your security operations and help you stay ahead of the curve.